UChecker – are you sure your libraries are up to date?
 When you see so many vulnerabilities being reported and so many security-related issues being exploited, you may think to yourself “I’m lucky not to be using that package or software, I’m not vulnerable to this”.
When you see so many vulnerabilities being reported and so many security-related issues being exploited, you may think to yourself “I’m lucky not to be using that package or software, I’m not vulnerable to this”.
Welcome to the world of software dependencies.
You may not be using curl/libcurl directly, but your browser sure is, even if you’re not aware of it. Or worse, your webserver is calling libcurl when it’s checking certificate chains in the backend. Or maybe it’s OpenSSL that’s being used to validate encrypted communications to your new application through a 3rd-party library you used.
Long story short, software developers are not fond of reinventing the wheel, and rightly so, and rely on tried and tested libraries to accomplish common-use scenarios like encryption, file management, communication, input validation, so on. This lets them focus on core application functionality. This is true for end-user applications as well as for server packages like databases, e-mail and web servers or artificial intelligence frameworks.
So, when those vulnerability reports come in, as so often happens, even apparently unrelated software can be exposed to them. So how can you know? It’s not very practical to go over the technical specifications of each application, or sometimes not even possible at all, how can you make sure you’re not using something vulnerable through a dependency of your applications?
This is where the KernelCare team stepped up, and created UChecker. It’s a tool that analyzes your system looking for vulnerable libraries being used by other applications, giving you a global look at packages that need to be updated as soon as possible. You will get detailed information regarding which program is using which vulnerable library.
Let’s take a look at UChecker in action:
|
curl -s -L https://kernelcare.com/uchecker | python |
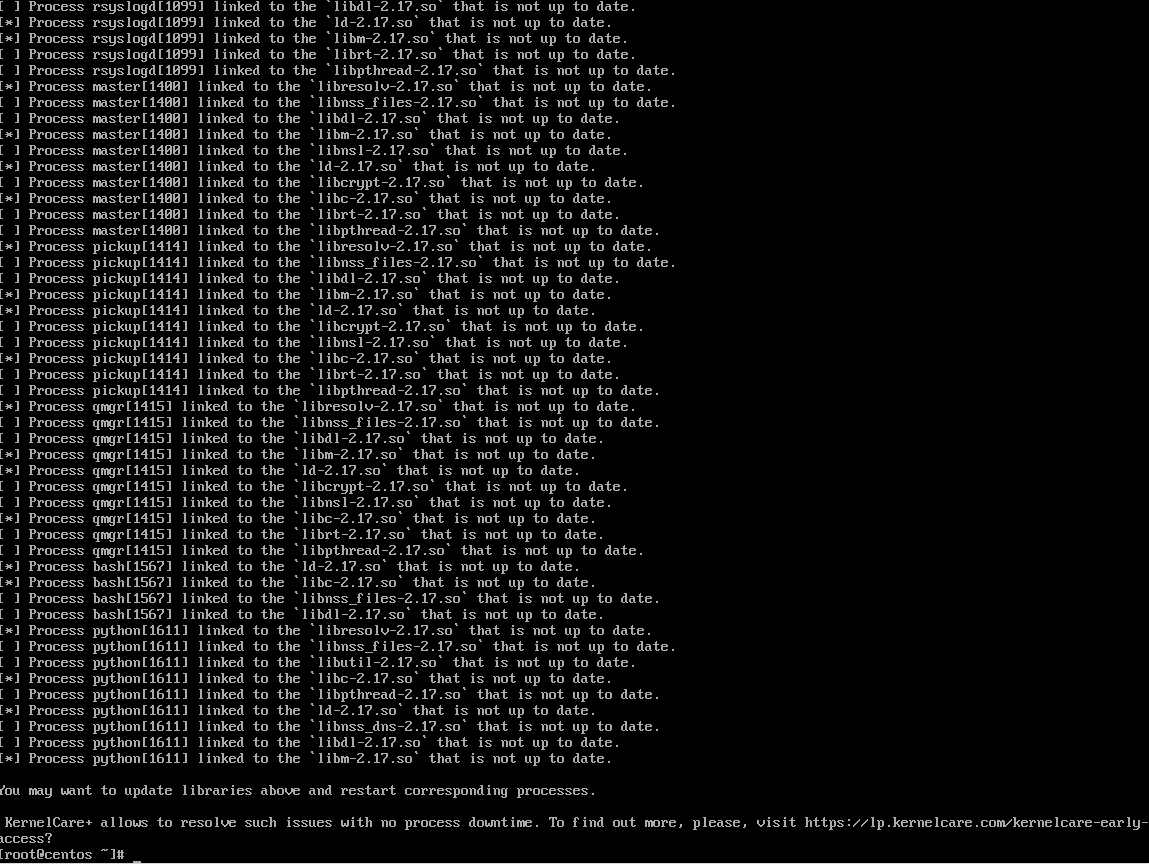
(UChecker running on a CentOS 7 fresh install, for demo purposes only. List intentionally shortened.)
And this means that this system needs to update several libraries. They are being called by multiple system services. You can simply update the affected libraries using your usual update tool.
Don’t forget to restart the affected services if your update tool fails to do so, because traditional update tools only touch the library files on disk, and any library already being used and currently residing in memory will continue to have the old code.
Unlike UChecker, other scanners wrongly check only on disk content for patch compliance and fail to spot in memory outdated versions, so you can be tricked into believing that your system is safe when it really isn’t.
After all the updates are done, this is the desired output:
UChecker is a free and open source tool you can use to validate your update mechanisms are working correctly. It can be integrated with tools like Nagios to alert you for systems running outdated libraries, or other monitoring and management tools. This can also help you prevent needless reboots by letting you know exactly which programs need to be restarted due to a vulnerable library update.
For added peace of mind, you could use KernelCare+ to receive updates automatically without having to restart applications, but even using UChecker alone will give you actionable information to improve your security awareness and patching process.

 Documentation
Documentation Login
Login



